General Information
The repository for this application (open on GitHub) has 10 stars and was forked 12 times. The codebase consists of 1644 lines of code and makes use of the following technologies:
Docker Eureka Hystrix Maven RabbitMQ Spring Config Turbine Zuul
Data Flow Diagram
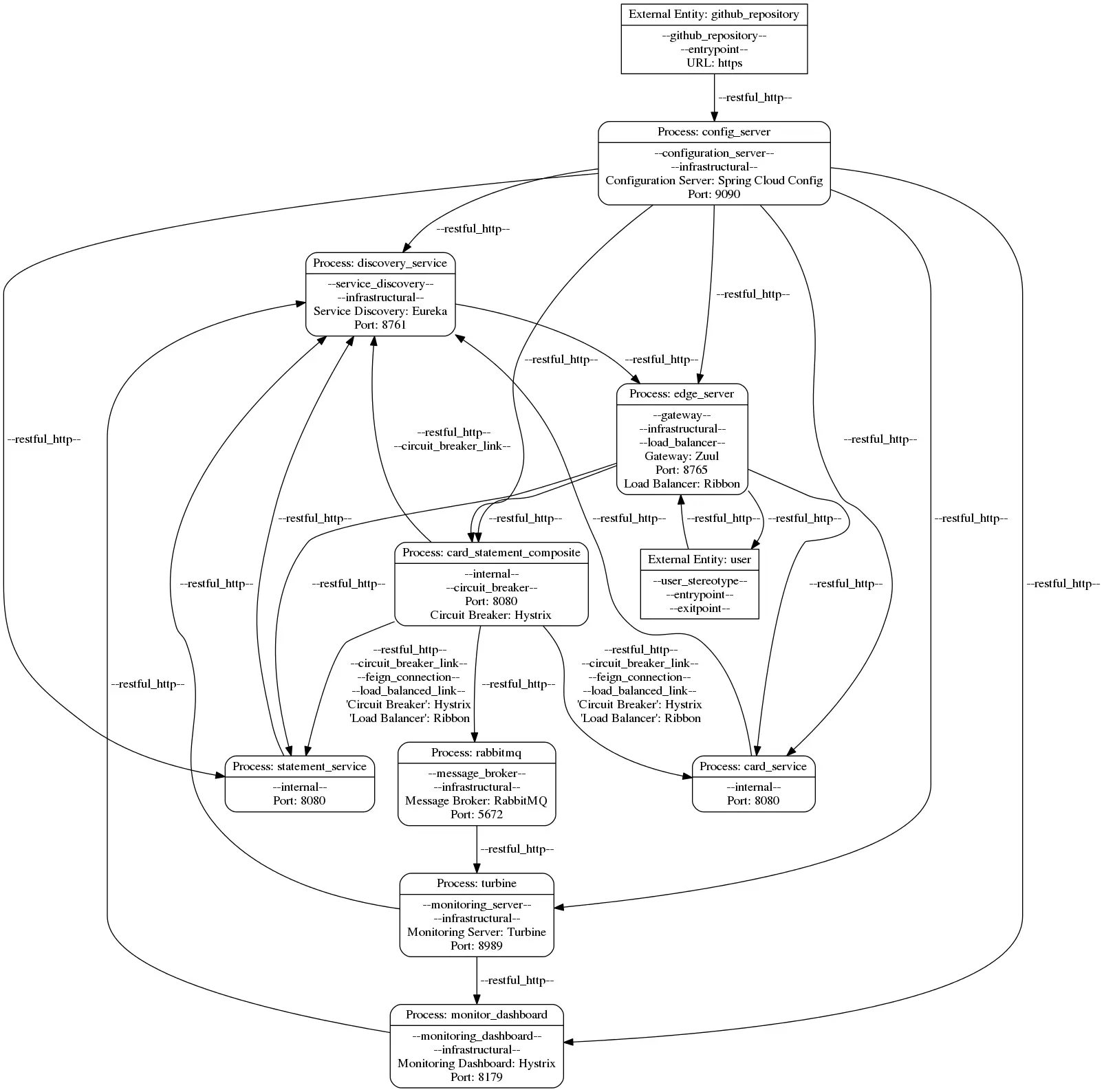
Download the following model file here. Other formats are provided below.
{
"services": [
{
"name": "config_server",
"stereotypes": [
"configuration_server",
"infrastructural"
],
"tagged_values": {
"Configuration Server": "Spring Cloud Config",
"Port": 9090
}
},
{
"name": "discovery_service",
"stereotypes": [
"service_discovery",
"infrastructural"
],
"tagged_values": {
"Service Discovery": "Eureka",
"Port": 8761
}
},
{
"name": "rabbitmq",
"stereotypes": [
"message_broker",
"infrastructural"
],
"tagged_values": {
"Message Broker": "RabbitMQ",
"Port": 5672
}
},
{
"name": "monitor_dashboard",
"stereotypes": [
"monitoring_dashboard",
"infrastructural"
],
"tagged_values": {
"Monitoring Dashboard": "Hystrix",
"Port": 8179
}
},
{
"name": "turbine",
"stereotypes": [
"monitoring_server",
"infrastructural"
],
"tagged_values": {
"Monitoring Server": "Turbine",
"Port": 8989
}
},
{
"name": "statement_service",
"stereotypes": [
"internal"
],
"tagged_values": {
"Port": 8080
}
},
{
"name": "card_service",
"stereotypes": [
"internal"
],
"tagged_values": {
"Port": 8080
}
},
{
"name": "card_statement_composite",
"stereotypes": [
"internal",
"circuit_breaker"
],
"tagged_values": {
"Port": 8080,
"Circuit Breaker": "Hystrix"
}
},
{
"name": "edge_server",
"stereotypes": [
"gateway",
"infrastructural",
"load_balancer"
],
"tagged_values": {
"Gateway": "Zuul",
"Port": 8765,
"Load Balancer": "Ribbon"
}
}
],
"external_entities": [
{
"name": "github_repository",
"stereotypes": [
"github_repository",
"entrypoint"
],
"tagged_values": {
"URL": "https://github.com/fernandoabcampos/microservices-config.git"
}
},
{
"name": "user",
"stereotypes": [
"user_stereotype",
"entrypoint",
"exitpoint"
],
"tagged_values": {}
}
],
"information_flows": [
{
"sender": "github_repository",
"receiver": "config_server",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "discovery_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "monitor_dashboard",
"receiver": "discovery_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "monitor_dashboard",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "turbine",
"receiver": "discovery_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "rabbitmq",
"receiver": "turbine",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "turbine",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "turbine",
"receiver": "monitor_dashboard",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "statement_service",
"receiver": "discovery_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "statement_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "card_service",
"receiver": "discovery_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "card_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "card_statement_composite",
"receiver": "discovery_service",
"stereotypes": [
"restful_http",
"circuit_breaker_link"
],
"tagged_values": {}
},
{
"sender": "card_statement_composite",
"receiver": "card_service",
"stereotypes": [
"restful_http",
"circuit_breaker_link",
"feign_connection",
"load_balanced_link"
],
"tagged_values": {
"'Circuit Breaker'": "\"Hystrix\"",
" 'Load Balancer'": "\"Ribbon\""
}
},
{
"sender": "card_statement_composite",
"receiver": "statement_service",
"stereotypes": [
"restful_http",
"circuit_breaker_link",
"feign_connection",
"load_balanced_link"
],
"tagged_values": {
"'Circuit Breaker'": "\"Hystrix\"",
" 'Load Balancer'": "\"Ribbon\""
}
},
{
"sender": "config_server",
"receiver": "card_statement_composite",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "card_statement_composite",
"receiver": "rabbitmq",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "discovery_service",
"receiver": "edge_server",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "user",
"receiver": "edge_server",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "edge_server",
"receiver": "user",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "config_server",
"receiver": "edge_server",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "edge_server",
"receiver": "card_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "edge_server",
"receiver": "statement_service",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
},
{
"sender": "edge_server",
"receiver": "card_statement_composite",
"stereotypes": [
"restful_http"
],
"tagged_values": {}
}
]
}
Model Items
The Application consists of a total of 110 elements:
| Element | Count |
|---|---|
| Services | 9 |
| External Entities | 2 |
| Information Flows | 24 |
| Annotations | 75 |
| Total Items | 110 |
Model Representations
Open the model in the following formats:
Traceability
Open the traceability information for all model items:
Security Rules
The following table shows the application’s adherence to the 17 architectural security rules. The last column provides model variants that adhere to the rule for each rule that is initially violated.
| Rule ID | Verdict | Evidence | Model Variant |
|---|---|---|---|
| R1 | Evidence | ||
| R2 | Evidence | Variant | |
| R3 | Evidence | Variant | |
| R4 | Evidence | Variant | |
| R5 | Evidence | Variant | |
| R6 | Evidence | Variant | |
| R7 | Evidence | Variant | |
| R8 | Evidence | Variant | |
| R9 | Evidence | Variant | |
| R10 | Evidence | Variant | |
| R11 | Evidence | Variant | |
| R12 | Evidence | Variant | |
| R13 | Evidence | ||
| R14 | Evidence | ||
| R16 | Evidence | ||
| R17 | Evidence | Variant | |
| R18 | Evidence | Variant |
Evidence and explanations for rule decisions
R1
Rule is partially adhered to: The application uses Spring Cloud Zuul as a single entry-point. There is no indication in the repository, that the API gateway does perform authentication/authorization for incoming requests.
Artifacts:
R2
Rule is violated: Services communicate internally over plain HTTP (See example artifacts). The communication is not authenticated.
Artifacts:
R3
Rule is violated: No authentication mechanism is deployed.
R4
Rule is violated: External entities are not represented in the application. Users behave transparent to the server. Note, that the server has a user-service, that is not used for authentication purposes.
R5
Rule is violated: No authentication tokens are used.
R6
Rule is violated: No rate limiting of any means is deployed.
R7
Rule is violated: User external entities can call the gateway service using an unencrypted HTTP connection.
Artifacts:
R8
Rule is violated: All internal services communicate over insecure HTTP connections.
Artifacts:
R9
Rule is violated: No central logging system is deployed.
R10
Rule is violated: No central logging system is deployed.
R11
Rule is violated: No logs are generated by the application.
R12
Rule is violated: RabbitMQ is deployed as a message broker between the circuit breaker and the monitoring server. It does not handle logging nor is the traffic encrypted and authenticated.
R13
Rule is adhered to: Hystrix is deployed as a circuit breaker in the service application and the gateway (see artifacts).
Artifacts:
- EdgeServerApplication.java: Line: 10
- CardServiceApplication.java: Line: 8
- StatementServiceApplication.java: Line: 8
R14
Rule is adhered to: The gateway server uses load balancing via Ribbon to access dependent services.
Artifacts:
- EdgeServerApplication.java: Line: 10
R15
This rule is not applicable: Not a service mesh deployment.
R16
Rule is adhered to:
- Registry Service (Eureka Server) with @EnableEurekaServer present.
- Started in Docker Container through Compose, thus deployable on dedicated server
Artifacts:
R17
Rule is violated: No HTTP basic password listed in any YML-Configuration of format username:password@here-location-of-eureka-server at “eureka.client.serviceUrl.defaultZone”.
Artifacts:
R18
Rule is violated: No secret manager is deployed. The deployed git configuration server is not a secrets manager.
Artifacts:
- ConfigServerApplication.java: Line: 8